Configuration – Automatos Remote Control Server
To access the “Automatos Remote Control Server” configuration menu, some settings can be applied in the package generated by our support team. If necessary, register a case in “” and inform the settings you want to apply when installing this module.
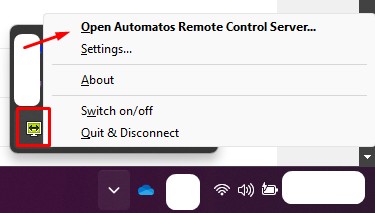
In the Systray, right-click on the “Automatos Remote Control Server” icon and “Open Automatos Remote Control Server
Initial settings
Access the advanced settings, change the language, and modify initial settings.
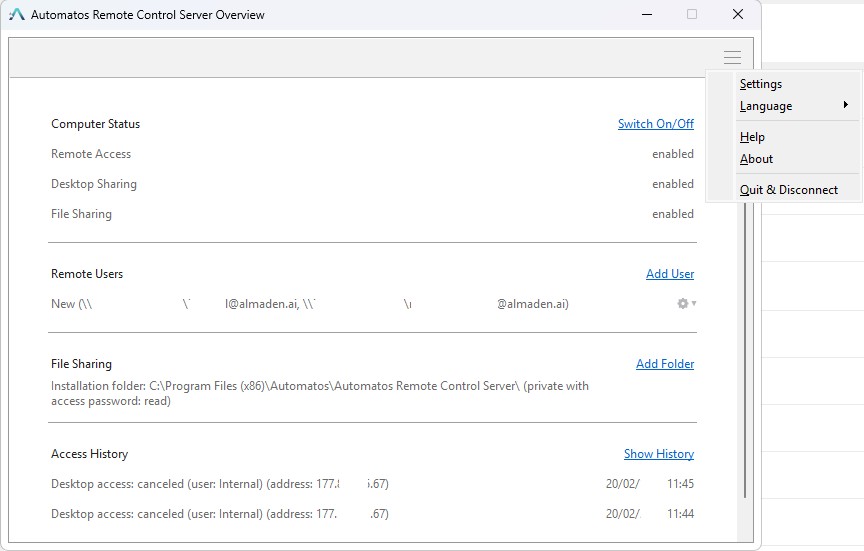
Computer Status
Allows enabling or disabling Remote Access Desktop Sharing, File Sharing
Remote Users
Displays which administrative account this package belongs to or was granted administrative permission.
File Sharing
Allows adding directories for file sharing.
Access History
History of successful, unsuccessful, or denied connection attempts.
Settings – Basic
These settings can only be accessed after elevating the administrator privileges on the user’s account.
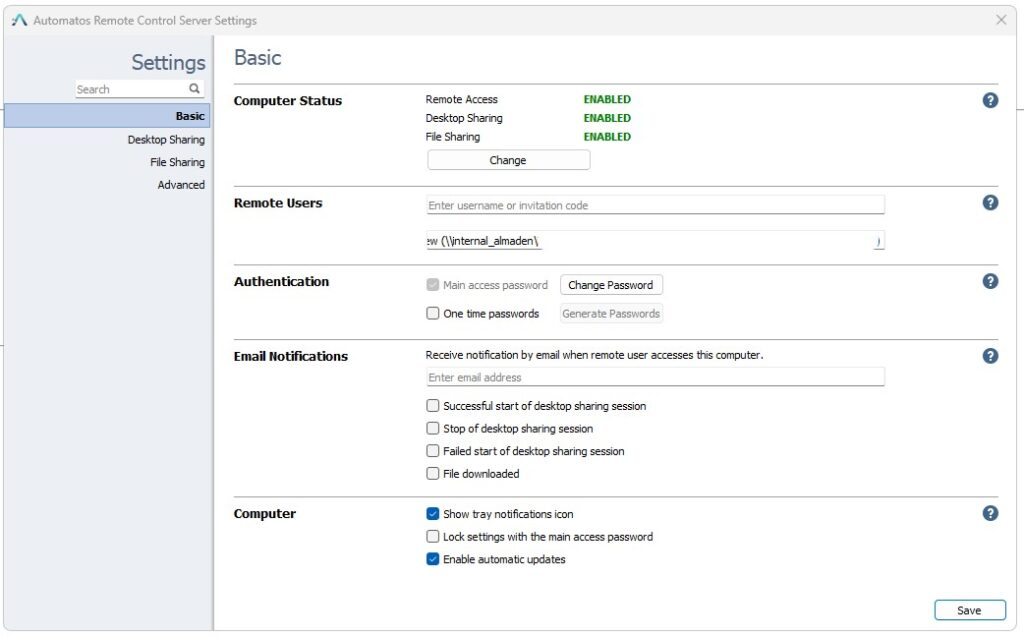
Computer Status
Allows enabling or disabling Remote Access Desktop Sharing, File Sharing
Remote Users
Displays which administrative account this package belongs to or was granted administrative permission.
Authentication
Main Access Password – Change the remote connection password (We do not recommend this change; if necessary to block user access, manage the computer groups and user groups).
One Time Passwords – Allows generating one-time remote connection passwords. Once a password is used to connect remotely, it expires, and a new one will be required for the next connection.
Email notifications
Sends notifications to the provided email address whenever an action is taken within the selected options.
Computer
Displays notifications in the systray, locks settings using the master password, and enables automatic updates for the “Automatos Remote Control Server.”
Settings – Desktop Sharing
Settings related to remote session sharing.
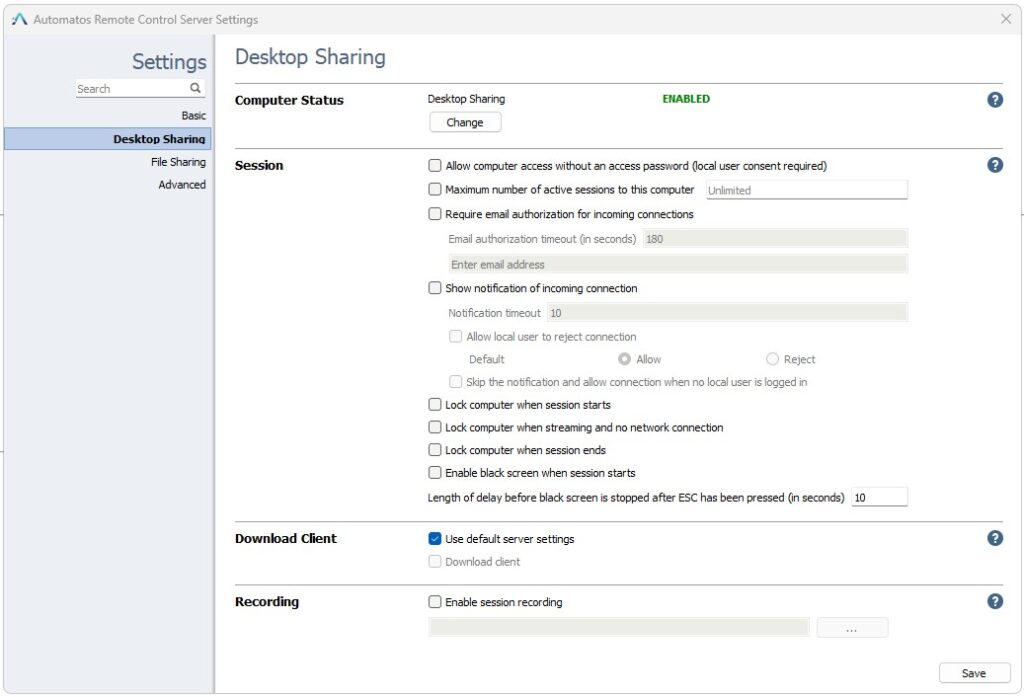
Computer Status
Displays the status of whether desktop sharing is enabled or disabled.
Session
Allow computer access without an access password (local user consent required)
Allows connection to this computer without the need for a remote connection password, only the user’s consent to allow the connection via a popup that is displayed.
Maximum number of active sessions to this computer
Allows limiting the number of users who can connect to this computer simultaneously (Each connection uses one active license).
Require email authorization for incoming connections
Requests confirmation via the provided email if the remote connection to this computer is authorized.
Show Notification of incoming connection
If this option is disabled, when a connection is made to this computer, it happens intrusively, and the user is not notified about the remote connection.
Notification Timeout
If “Remote session settings (Recommended to keep default).
Allow User Reject Connection” is enabled, it allows the user of this computer to accept the remote connection without an option to refuse, or the “Reject” option will be displayed so they can deny the remote connection.
Show Notification of incoming connection
If this option is disabled, when a connection is made to this computer, it happens intrusively, and the user is not notified about the remote connection.
Notification Timeout
If “Show Notification of incoming connection” is enabled, a confirmation prompt will be displayed to the user with a defined time (in seconds) for them to confirm the remote connection.
Skip the notification and allow connection when no local user is logged in
By enabling this option, the remote connection will not require the user’s approval and cannot be rejected when no account is logged into the computer.
Lock computer when session starts
Locks this computer when a remote session starts.
Lock computer when streaming and no network connection
If the computer loses internet connection during the session, the session will be locked.
Lock computer when session ends
Locks the session when the remote connection is ended.
Enable black screen when session starts
The screen will turn black for the user of the computer when a remote session starts.
Download Client
Use Default server settings – Keeps the applied settings for user accounts in “remote.automatos.com” > Administrative > Users.
Download client – Permanently disabled.
Recording
Enable Session recording – When enabling and configuring the directory, all remote connection sessions will be recorded.
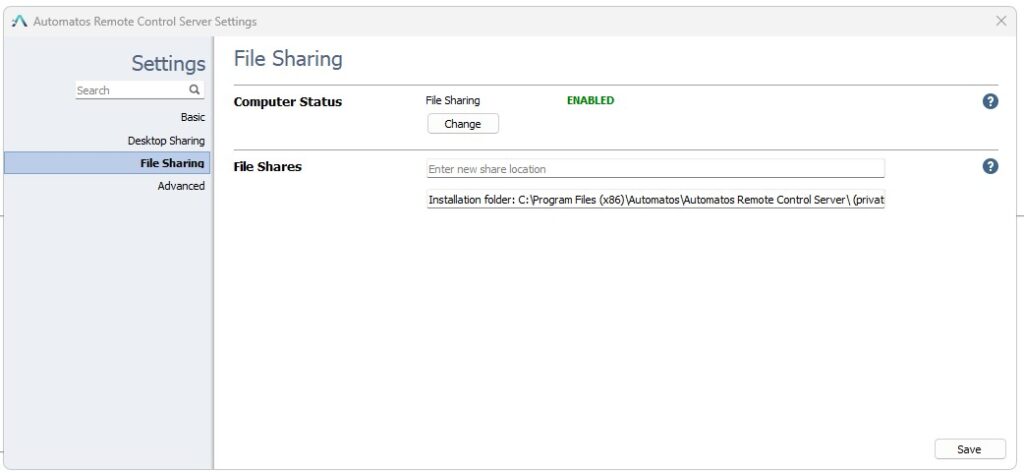
File Sharing
Computer Status
File Sharing – Displays the execution status, enabled or disabled.
Files Shares
Files Shares – When enabling and configuring the directory, all remote connection sessions will be recorded.
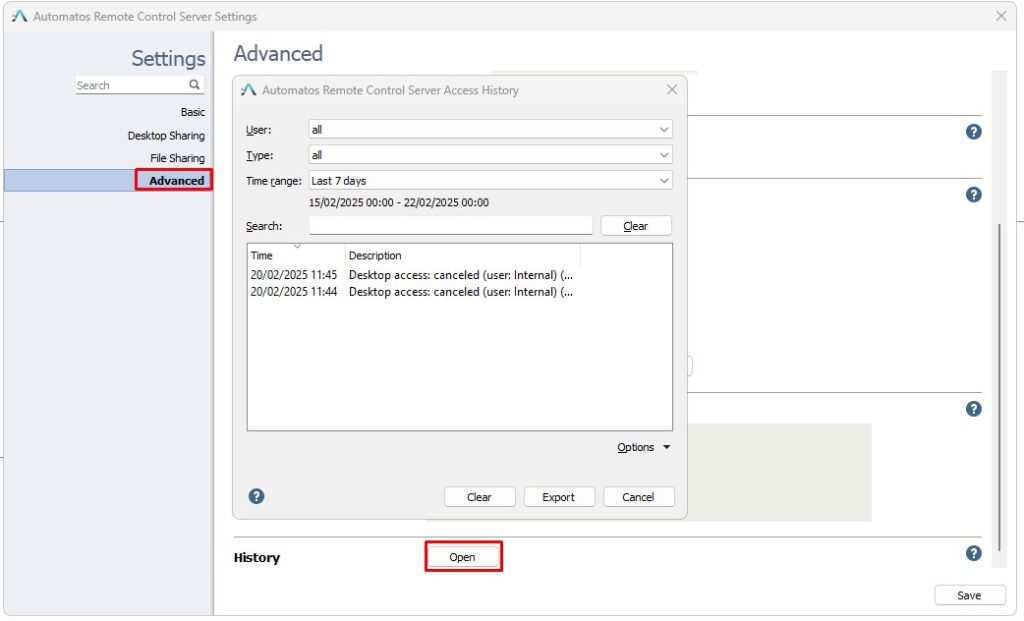
Advanced
The additional options Tunnel Connection, Attach Session, and Sleep Mode are disabled.
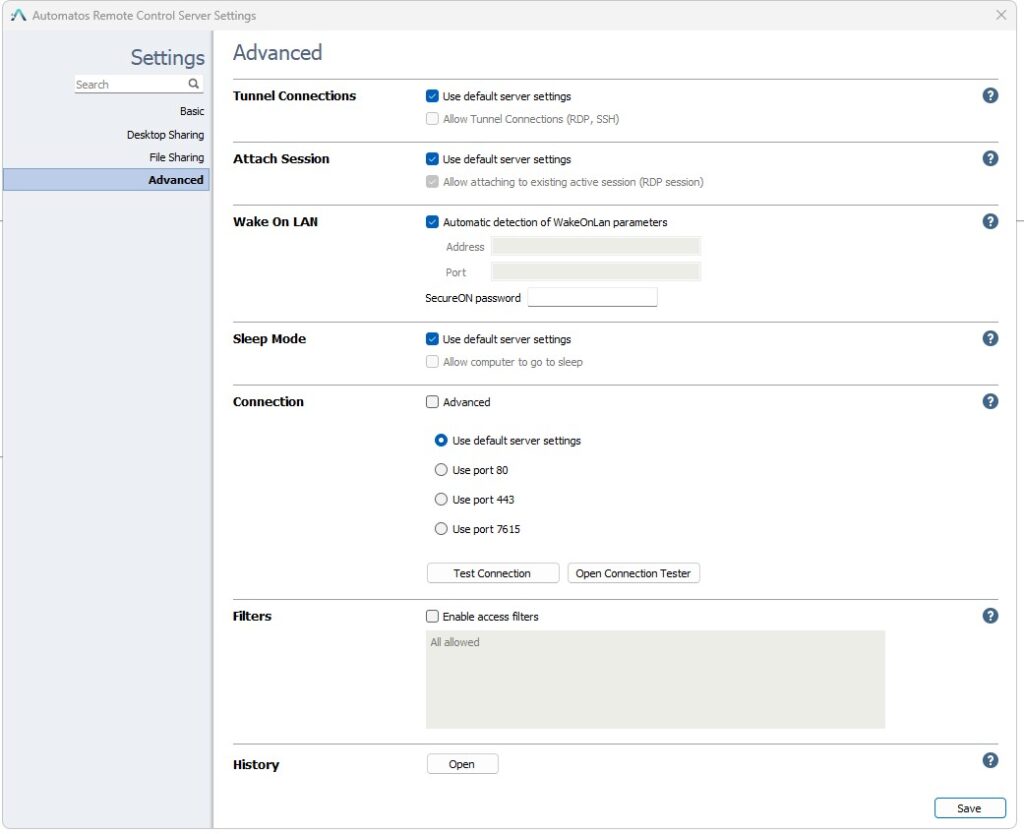
Wake on Lan
Allows waking up devices that have the Wake on LAN feature enabled in the BIOS (refer to the technical information for this feature in computing systems).
Connection
Use Default Server Settings – Keep as default, change these options only in extreme necessity and with the guidance of Almaden analysts.
Filters
This feature blocks or allows connections to the computer from networks, IPs, or Mac Addresses that are defined.
Enable – When enabling this feature, you need to specify which rule to apply according to the syntax (Using Filters).
Using Filters
You can enable get code filters that limit access based on the IP and/or MAC address – you can set it for a domain or for a specific user.
Each filter definition consists of pairs of filter name and filter descriptions. Pairs are delimited with a new line or using the “;” character.
Filter syntax:
(allow_|deny_)(all|ip|mac) <filter description> [;(allow_|deny_)(ip|mac) <filter description 1> ...]
First part of the pair begins with allow_ or deny_ and is followed by ip or mac (applying IP or MAC filtering). The second part (filter_description) depends on the filtering type – either an IP address/subnet/… or a MAC address using the aa-bb-cc-dd-ee format.
When accessing a computer, its access rules are read from the top down and stop immediately when a rule is matched, whether it is allow or deny. If it gets to the bottom of the list, deny_all is implicitly used – i.e. if all the rules fail to match and it gets to the bottom of the list, access is denied. This means that you do not need to append deny_all to your list.
An example:
deny_ip 192.168.0.113
allow_ip 192.168.0.112/255.255.255.0
allow_mac 00-19-d1-06-c9
This will allow connections from any IP in the 192.168.0.* subnet except 192.168.0.113 and allow connections coming from the 00-19-d1-06-c9 MAC address with any IP.
Note: IP and MAC addresses can be spoofed, so never base your security solutions only on that.
History
View the history of successful, failed, and rejected connections to the computer.